Cisco FTD Interview Questions and Answers
Ques1. What does FTD and FMC stand for?
FTD stands for Firepower Threat Defense.
FMC stands for Firepower Management Center
Ques2. What is the usage and purpose of FMC?
FMC is used for managing the SFR and FTD devices.
Ques3. Please elaborate the difference between a prefilter rule and an access rule?
Below table enlists difference between Prefiltering and Access control –

Ques4. Can ASA 5500-X Series have the NGIPS SFR?
Yes, Cisco ASA 5500-X Series can have SFR module in it.
Ques5. Where can you install and run the SFR in ASA?
SFR NGIPS can be installed and operated on an SSD in an ASA.
Ques6. In order to reimage ASA 5506-X hardware to FTD, what is the correct order? i. Upgrade the ROMMON software.
ii. Reload the ASA hardware with a boot image.
iii. Install the FTD system software.
iv. Copy the image files to a server.
The correct workflow is to
(a) Copy the image files to a server, then
(b) Upgrade the ROMMON software, next
(c) Reload the ASA hardware with a boot image and finally
(d) Install the FTD system software
Ques7. To verify if SSD is installed on ASA hardware, which command should be executed? Command to confirm whether an SSD is install on ASA hardware is –
Show inventory
Ques8. In which component of Firepower 4100 Series is FTD software installed?
FTD software in Firepower 4100 Series is installed in Security Engine
Ques9. Which interface on an ASA device is assigned with an IP address during FTD software initialization?
The interface is br1
Question10. When selecting the type of traffic, if mgmt is selected then what would be the result?
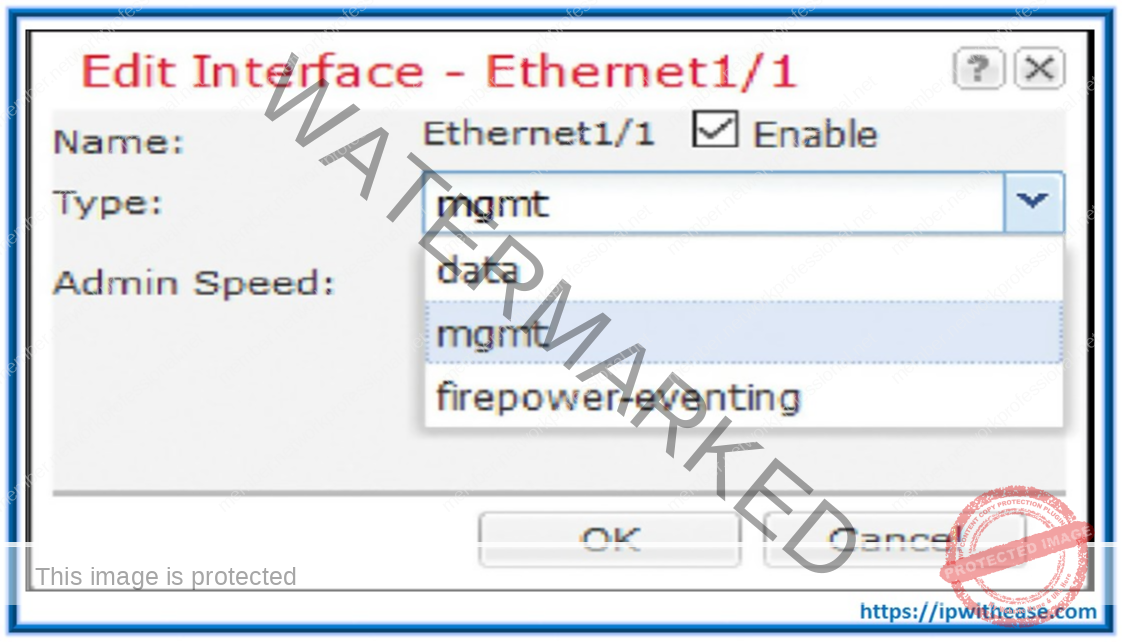
If we want to select an interface for management communication between an FTD and FMC, then mgmt should be selected.
Quest11. Which interface is shown as “?” in lower-end and midrange ASA 5500-X series models?

The pointed interface is Management Interface
Ques12. What is the name of the Mgmt interface which CLI shows, when connected to Firepower Code and when connected to ASA code?

When it is connected to Firepower code, CLI shows as br1.
When it is connected to ASA code, CLI shows as Management x/x.
Which command is used in FTD to view the statistics of events inside the encrypted
Ques13.
tunnel between FTD and the FMC?
The command used in FTD to view the statistics of events inside the encrypted tunnel between FTD and the FMC is sftunnel-status
Ques14. Which command confirms whether FTD is registered with the FMC?
Commands used to confirm and check the status of whether FTD is registered with FMS is
show managers
Ques15. Which command is used to configure a manager in an FTD?
Command used to configure a manager in FTD is
configure manager add <IP_Address_of_FMC> <Registration_Key> <NAT_ID>
Ques16. What are the capabilities of the Firepower in terms of Licenses?
There are four types of Licenses in FTD –
-
Base
-
Threat
-
Malware
-
URL Filtering
Ques17.
Describe the usage and functionality of Base and Threat Licenses?
Base License:
o Update the Firepower system
o Control applications and users
o Perform switching, routing, and NAT
Threat License:
o Detect and prevent intrusion attempts o Blacklist traffic based on intelligence o Block transfer of certain types of files
Describe the usage and functionality of Malware and URL Filtering licenses?
Malware License:
o Protect the network from malware, enable AMP for the network, and enable AMP Threat Grid features
URL Filtering:
o Filter URLs based on reputation and category
If we go to the System > Licenses > Smart Licenses page, we see Evaluation Mode
Ques18.
Ques19. If we go to the System > Licenses > Smart Licenses page, we see Evaluation Mode button. What is the time period of the evaluation mode?

The time period of evaluation mode is 90 days once it is started.
Ques20. What happens when we turn on the Evaluation Mode on the Firepower System?
If we turn on the Evaluation Mode on the Firepower System, it enables all the security features on the FMC. You can apply these features on FTD for a 90-day period. Before the evaluation
period expires, we must purchase a valid license and register the FMC with the Cisco License Authority for continuous operation.
Ques21. What is the workflow to Purchase, Generate, and Apply a Smart License in Firepower System?
Below is the stepwise workflow –

Ques22. What is the behaviour of FTD when it is deployed in a Routed Mode?
In Routed Mode, FTD performs like a Layer 3 device. Each interface on an FTD device connects to a different subnet. If FTD is configured in a routed mode then each interface can act as a gateway for the subnet it is in and can route the traffic from one subnet to another.
Ques23. If you want to install FTD Version 6.1 on Firepower 9300 appliance having FXOS Release 1.1.4, what is the correct order of action?
Install FXOS Release 2.0.1 and then install FTD Version 6.1
Ques24. Which file can be deployed directly into an ESXi host if we are installing/running FMC?
OVF
Ques25. Which command syntax would be correct, if we want to ping test from FTD to the FMC?
Ping system IP_Address
Ques26. Which port does the Firepower System use for management communication by default?
Firepower system uses TCP Port 8305 for management communication by default.
Ques27. If we hit enter in the highlighted prompt, what would be the default firewall mode?

The default firewall mode would be Routed mode.
Ques28. In below snippet, when registration with the manager is completed, the IP 10.1.1.16 is
of which device?

The IP 10.1.1.16 is the IP address of the Manager with which FTD box is connected successfully.
Ques29. Which command is used to configure FTD from Transparent Mode to Routed Mode?
Configure firepower routed
Ques30. What is the behaviour of FTD when it is deployed in a Transparent Mode?
In Transparent Mode, FTD bridges the inside and outside interfaces into a single Layer 2 network and remains transparent to the hosts. When FTD is in Transparent Mode, we cannot assign an IP address to any interface of FTD.
Ques31. In what mode firewall is configured in below snippet?

Firewall is configured in transparent mode.
Ques32. In what scenario do Gig interfaces and BVI interface have same IP?

This happens when firewall is configured in transparent mode.
Ques33. Which command provides an overview of the various components of an inline interface set?
Show inline-set
Ques34. What is the first-level-defense mechanism implemented on Firepower Engine?
Security Intelligence is a first-level-defense mechanism implemented on Firepower Engine. Ques35. Which directory stores the filed related to DNS Policy?
/var/sf/sidns_download stores the filed related to DNS Policy
Ques36. Which licenses are necessary to block a URL based on its category and reputation?
Threat and URL Filtering licenses are necessary to block a URL based on its category and reputation.
Ques37. Which type of analysis requires a connection to the cloud?
Sandbox
Ques38. Which base policy enables the largest number of standard text Snort rules by default?
Security over Connectivity enables the largest number of standard text Snort rules by default. Ques39. Which NAT section has highest priority during rule evaluation?
NAT Rules Before has highest priority during rule evaluation
Ques40. After you deploy a new NAT policy, if a connection still uses a rule from the prior version of the NAT policy, how could you ensure that FTD will use the new policy?
We would need to clear the current translation table.
Ques41. What is Security Intelligence?
Security Intelligence is a first line of defense against malicious internet content. Using security intelligence, FTD can black connections based on
-
IP addresses
-
DNS reputation and URLs.
Ques42. What is the function of Network Analysis Policy?
A Network Analysis Policy governs how traffic is decoded and preprocessed so it can be further evaluated, especially for anomalous traffic that might signal an intrusion attempt.
Ques43. What is the function of Intrusion Policy?
An intrusion policy uses intrusion and preprocessor rules to scan the decoded packets for attacks based on patterns. Intrusion policies are paired with variable sets, which allow you to use named values to precisely reflect your network environment.
Ques44. What is Access Control Rule Monitor Action?
The Monitor action does not disturb traffic flow; matching traffic is neither immediately permitted nor denied. Rather, traffic is matched against additional rules to determine whether to permit or deny it. The first non-Monitor rule matched decides traffic flow and any further inspection. If there are no additional matching rules, the system uses the default action.
Ques45. What is Access Control Rule Trust Action? What is Access Control Rule Blocking Actions?
The “Trust” action allows traffic to pass without deep inspection or network discovery. Trusted traffic still has to pass through identity requirement and rate limiting.

“Block” and “Block with reset” actions will deny traffic without need of inspecting the traffic. “Block with reset” rules also reset the connection.

Ques46. What is Access Control Rule Interactive Blocking Actions?
The Interactive Block and Interactive Block with reset actions give users a chance to bypass a website block by clicking through a customizable warning page, called an HTTP response page. Interactive Block with reset rules also reset the connection.
Ques47. What is the function of Network Discovery Policies? What are 2 types of Network Discovery mechanisms?
The Network Discovery Policy on the Firepower Management Center controls how the system collects data on your organization’s network assets and which network segments and ports are monitored.
The 2 types of Network Discovery methods are Active and Passive. In case of Active network discovery, we are required to run Nmap scanner feature in FMC for discovery of hosts and applications in network. Further, Active detection adds host information collected by active sources to network maps where Nmap discovers operating systems and applications on hosts. Passive Network discovery does not make use of Nmap scanner and waits to sniff for the Hosts and Applications that are running in the network.
Ques48. What is the purpose of Firepower Recommended Rules?
Firepower recommended rules are used to relate and associate the server, network devices, applications, operating systems and protocols detected in our network with the rules written to protect these assets. Firepower recommended us the rules which should be enabled so that it can protect all the related protocols and applications which are running in our network.
Ques49. How many connectivity models are there for network analysis and intrusion policies in Firepower System?
Balanced Security and Connectivity network analysis and intrusion policies Connectivity over Security network analysis and intrusion policies
Security over Connectivity network analysis and intrusion policies Maximum Detection network analysis and intrusion policies
No Rules Active intrusion policy
Describe Balanced Security and Connectivity network analysis and intrusion policies?
Ques50.
These policies are built for both speed and detection. This is a balanced type of policy in which security and connectivity is treated equally important. The default policy in FTD is also this one.
Ques51. Describe Maximum Detection network analysis and intrusion policies?
These policies are built for organizations where network infrastructure security is given even more emphasis than is given by the Security over Connectivity policies, with the potential for even greater operational impact. For example, the intrusion policy enables rules in a large number of threat categories including malware, exploit kit, old and common vulnerabilities, and known in-the-wild exploits.
Ques52. Describe No Rules Active intrusion policy?
In the No Rules Active intrusion policy, all intrusion rules and advanced settings are disabled. This policy provides a starting point if you want to create your own policy for intrusion instead of basing it on the enabled rules in one of the other system-provided policies.
- General Interview Preparation
- Network Phone Interview Questions
- Network F2F Interview Question
- Company Interview Questions
- Troubleshooting Questions
- How to Own an Interview
- Wireless Interview Questions
- Security Interview Questions
- Technical Scenario Interview Tips
- Company Projects for Interviews
- SDWAN Interview Questions
- Cyber Interview Questions
- Network Automation Interview Questions
- VPN Top 100 Interview Questions and Answers
- 50 Cloud Engineer Interview Questions and Answers
- ASA Firewall Interview Questions and Answers
- CEH Interview Questions and Answers
- Cisco FTD Interview Questions and Answers
- Wireless Interview Questions & Answers